A technique that can be used to bypass AV/EDR memory scanners. This can be used to hide well-known and detected shellcodes (such as msfvenom) by performing on-the-fly decryption of individual encrypted assembly instructions github.com/vxCrypt0r/Vo...
A technique that can be used to bypass AV/EDR memory scanners. This can be used to hide well-known and detected shellcodes (such as msfvenom) by performing on-the-fly decryption of individual encry...
Develop your own C# Obfuscator www.ribbiting-sec.info/posts/2024-0...
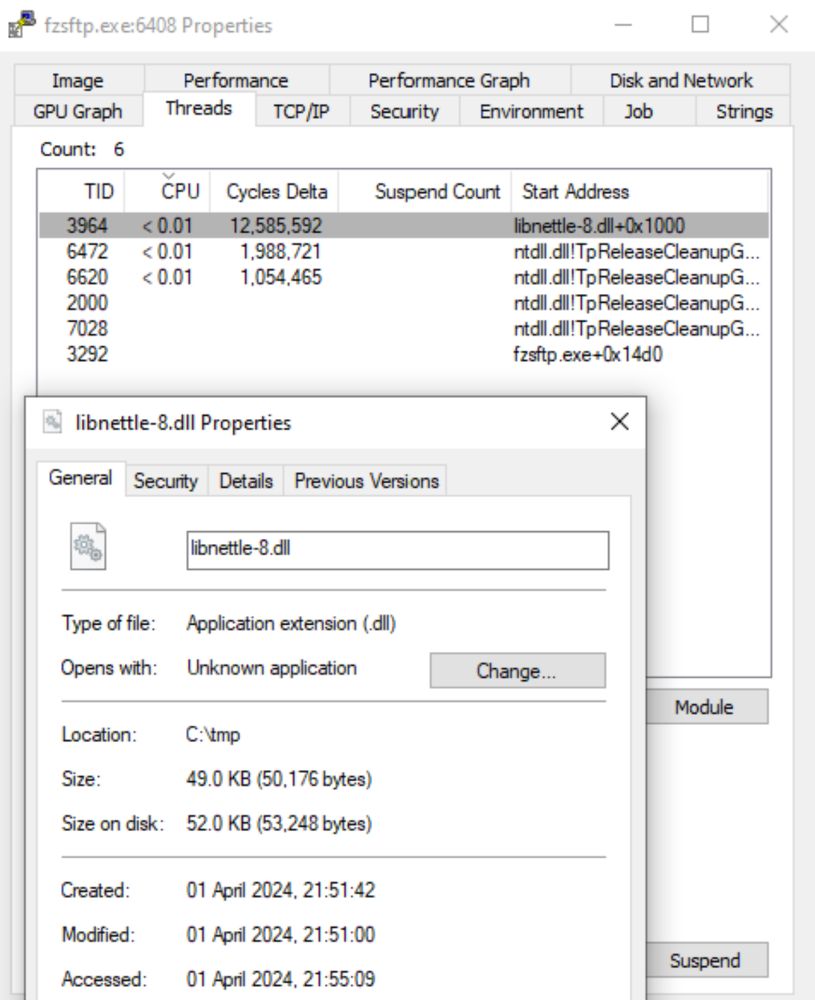
Injecting code into PPL processes without vulnerable drivers on Windows 11 blog.slowerzs.net/posts/pplsys...

EDRaser - a powerful tool for remotely deleting access logs, Windows event logs, databases, and other files on remote machines github.com/SafeBreach-L...
EDRaser is a powerful tool for remotely deleting access logs, Windows event logs, databases, and other files on remote machines. It offers two modes of operation: automated and manual. - SafeBreach...
Sharp post-exploitation toolkit providing modular access to the Microsoft Graph API for cloud and red team operations github.com/mlcsec/Sharp...
Microsoft Graph API post-exploitation toolkit. Contribute to mlcsec/SharpGraphView development by creating an account on GitHub.
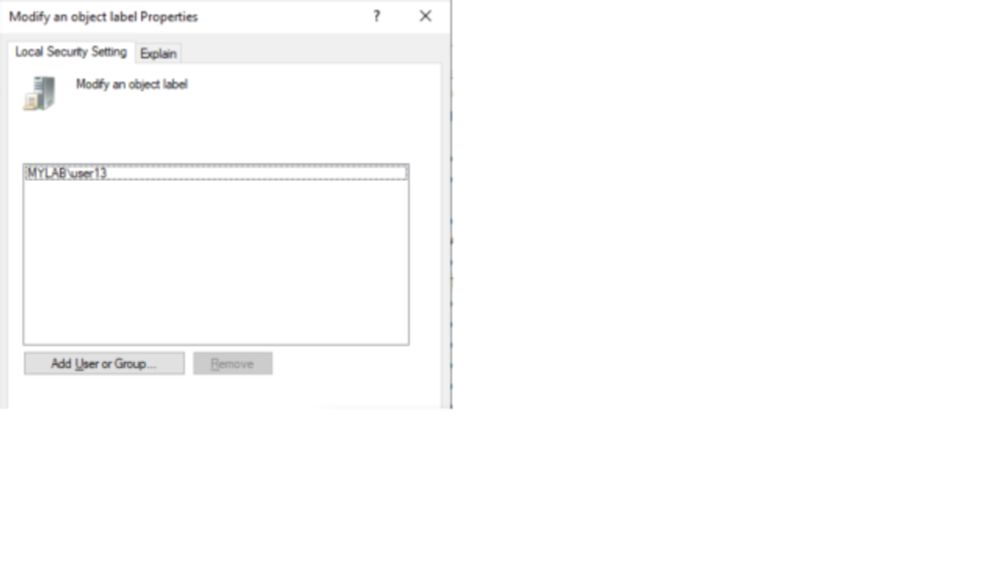
A Post-Compromise granular, fully reflective, simple and convenient .NET library to embed persistence by abusing Security Descriptors of remote machines. github.com/cybersectrol...
Contribute to cybersectroll/SharpPersistSD development by creating an account on GitHub.