Uncompressing Dilithium’s public key (Paco Azevedo Oliveira, Andersson Calle Viera, Benoît Cogliati, Louis Goubin) ia.cr/2024/1373
Benchmarking Attacks on Learning with Errors (Emily Wenger, Eshika Saxena, Mohamed Malhou, Ellie Thieu, Kristin Lauter) ia.cr/2024/1229
Adaptively Secure 5 Round Threshold Signatures from MLWE/MSIS and DL with Rewinding (Shuichi Katsumata, Michael Reichle, Kaoru Takemure) ia.cr/2024/1033
Flood and Submerse: Distributed Key Generation and Robust Threshold Signature from Lattices (Thomas Espitau, Guilhem Niot, Thomas Prest) ia.cr/2024/959
Two-Round Threshold Signature from Algebraic One-More Learning with Errors (Thomas Espitau, Shuichi Katsumata, Kaoru Takemure) ia.cr/2024/496
Evaluating the security of CRYSTALS-Dilithium in the quantum random oracle model (Kelsey A. Jackson, Carl A. Miller, Daochen Wang) ia.cr/2023/1968
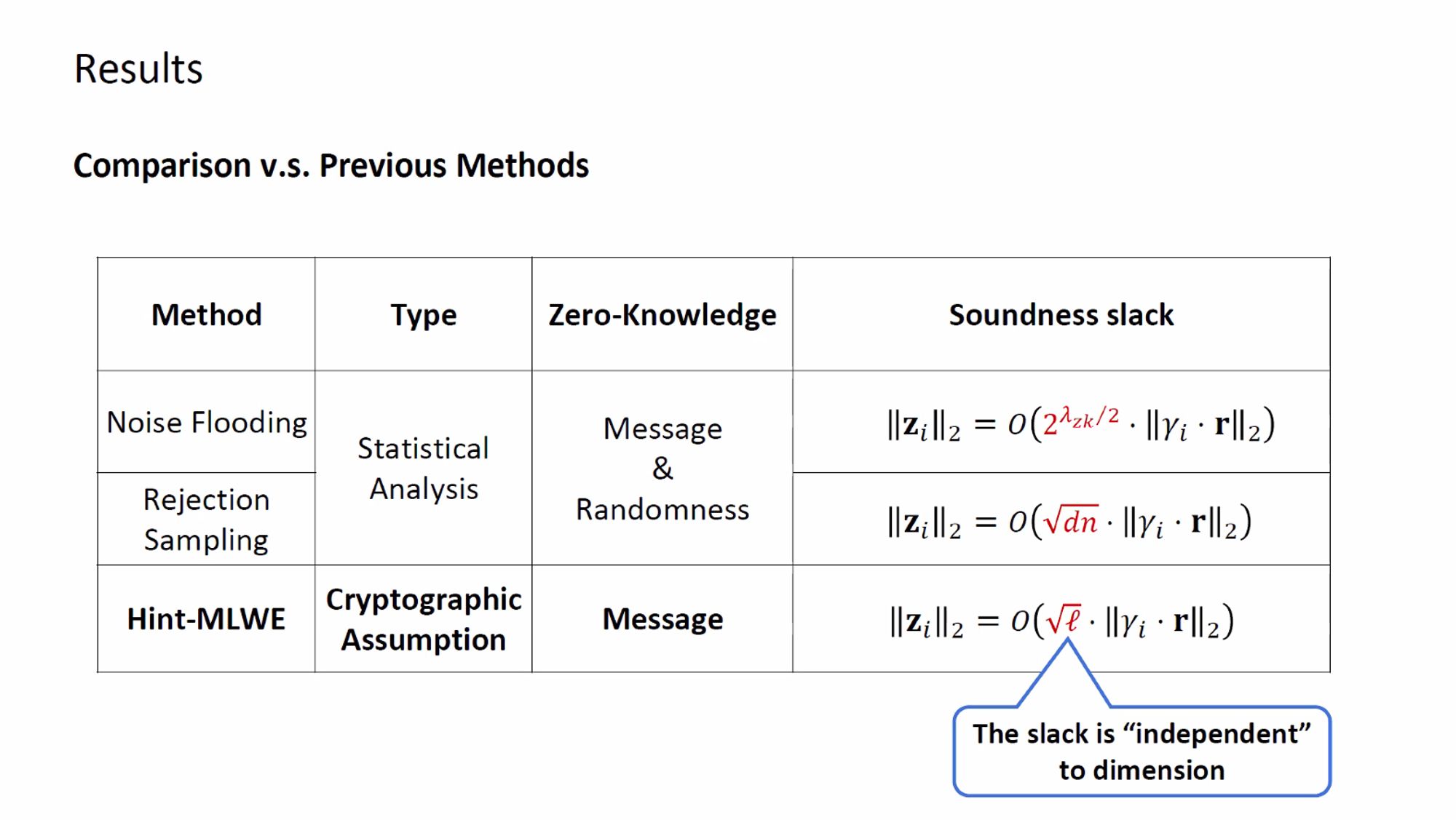
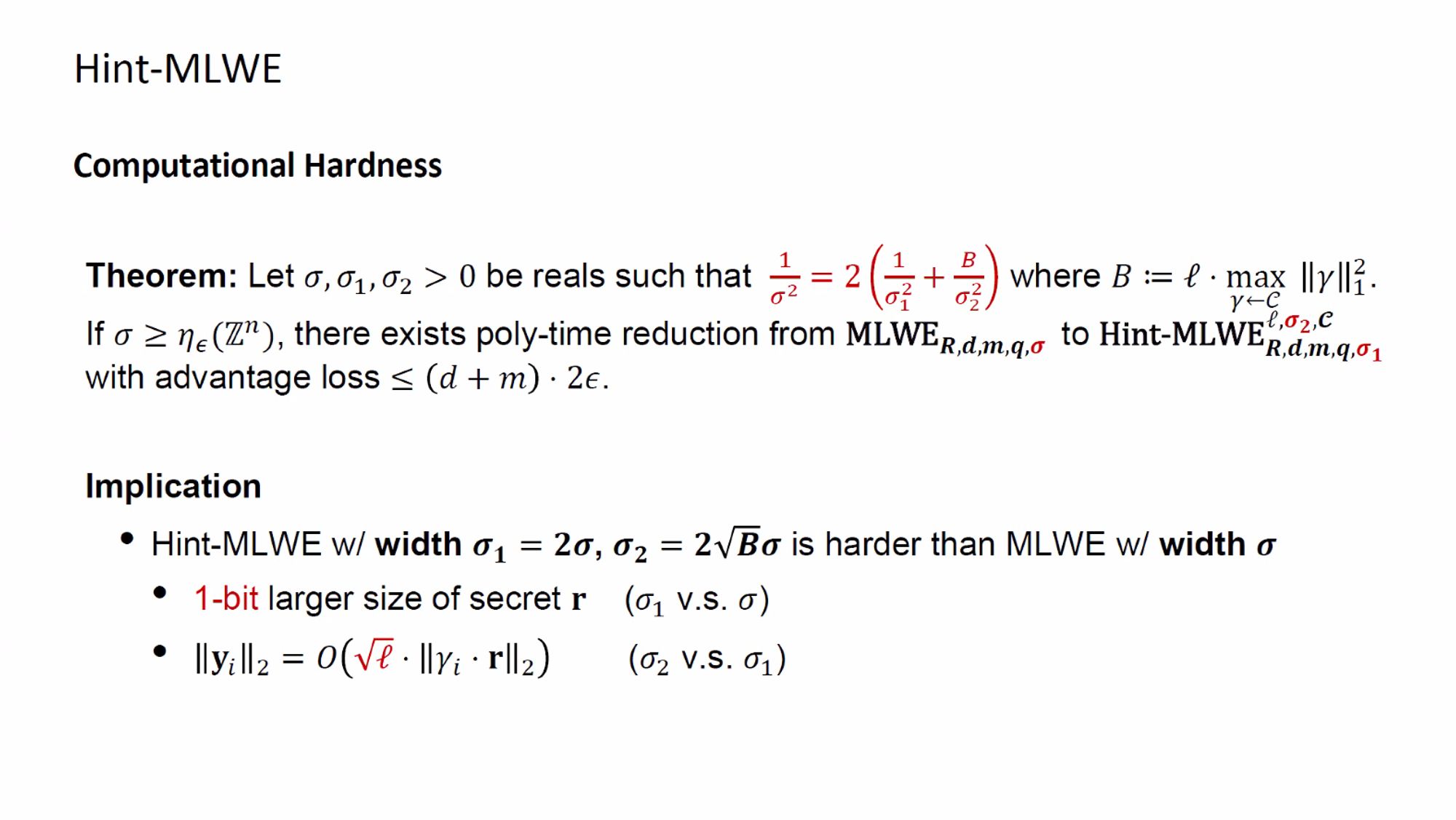
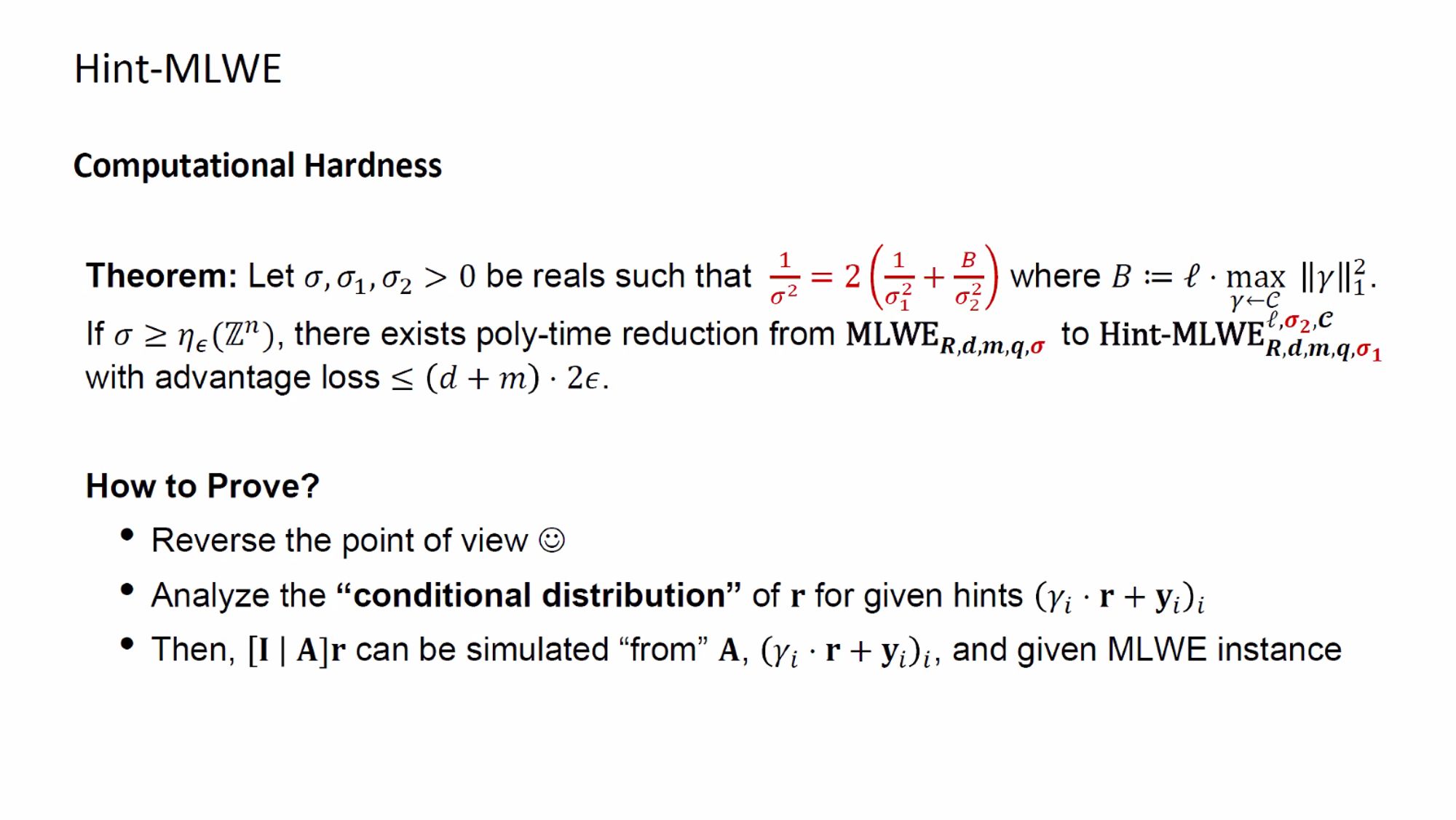
Q: Concrete security? A: Concrete security of Hint-MLWE relies on that of MLWE.