Pro-Ukrainian Hackers Strike Russian State TV on Putin's Birthday #thehackersnews

Ukraine claims cyber attack on Russian state media VGTRK, disrupting operations and wiping server data.
Qualcomm Urges OEMs to Patch Critical DSP and WLAN Flaws Amid Active Exploits #thehackersnews
Qualcomm fixes 20 vulnerabilities, including actively exploited CVE-2024-43047 in DSP, urging fast OEM updates.
E.U. Court Limits Meta's Use of Personal Facebook Data for Targeted Ads #thehackersnews

EU court orders Meta to restrict Facebook user data for ads, enforcing GDPR limits on personal data use.
Apple Releases Critical iOS and iPadOS Updates to Fix VoiceOver Password Vulnerability #thehackersnews

Apple's iOS 18.0.1 fixes a VoiceOver password vulnerability and an audio bug in iPhone 16. Update now!
Google Adds New Pixel Security Features to Block 2G Exploits and Baseband Attacks #thehackersnews

Google enhances Pixel security in Android 14 to block baseband attacks, 2G downgrades, and SMS Blaster fraud.
Ivanti Endpoint Manager Flaw Actively Targeted, CISA Warns Agencies to Patch #thehackersnews

Critical Ivanti Endpoint Manager flaw CVE-2024-29824 actively exploited. CISA urges immediate updates to secure networks
Fake Trading Apps Target Victims Globally via Apple App Store and Google Play #thehackersnews

Cybercriminals use fake trading apps on Apple and Google stores for global "pig butchering" scam, exploiting victim trust through official channels.
Researchers Sound Alarm on Active Attacks Exploiting Critical Zimbra Postjournal Flaw #thehackersnews

Urgent patching is needed for Zimbra Collaboration as attackers exploit CVE-2024-45519 to execute commands.
PyPI Repository Found Hosting Fake Crypto Wallet Recovery Tools That Steal User Data #thehackersnews
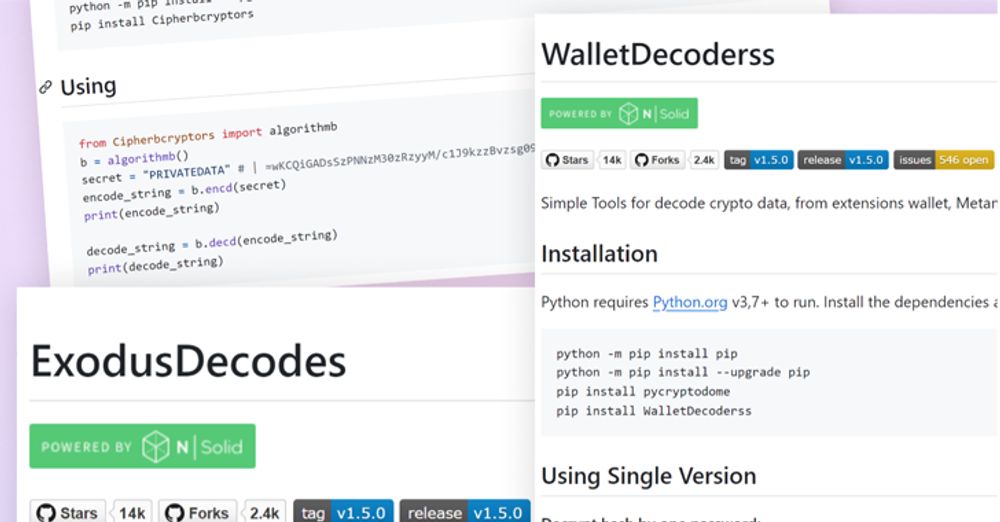
Malicious PyPI packages disguised as crypto wallet tools steal sensitive data, targeting popular wallets like Trust and MetaMask.
New Cryptojacking Attack Targets Docker API to Create Malicious Swarm Botnet thehackernews.com/2024/10/new-... via @TheHackersNews

Hackers exploit Docker API to build botnet, using Docker Swarm and cryptojacking malware to compromise cloud hosts.