Secrets and Shadows: Leveraging Big Data for Vulnerability Discovery at Scale: billdemirkapi.me/leveraging-b...#bigdata#cloud#iass#vulnerability#cybersecurity#informationsecurity#exploitation

Modern technologies like the cloud have made rapidly developing scalable software more accessible than ever. What risks has cloud computing introduced for the sake of convenience?
Red Teaming in the age of EDR: Evasion of Endpoint Detection Through Malware Virtualisation: blog.fox-it.com/2024/09/25/r...#edr#evasion#malware#cybersecurity#informationsecurity#reverseengineering#programming
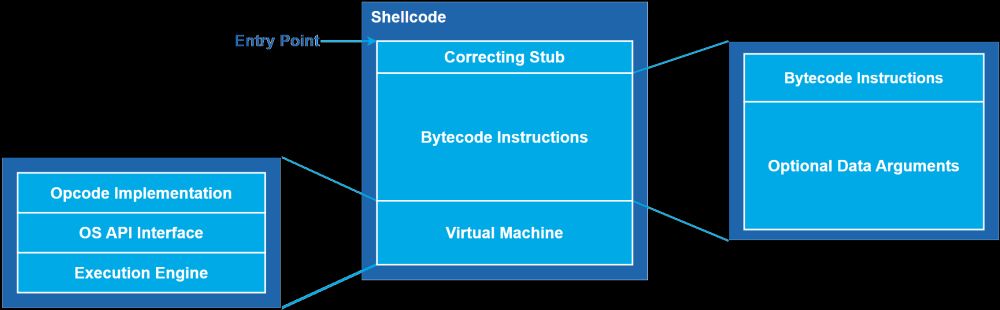
Authors: Boudewijn Meijer && Rick Veldhoven Introduction As defensive security products improve, attackers must refine their craft. Gone are the days of executing malicious binaries from di…
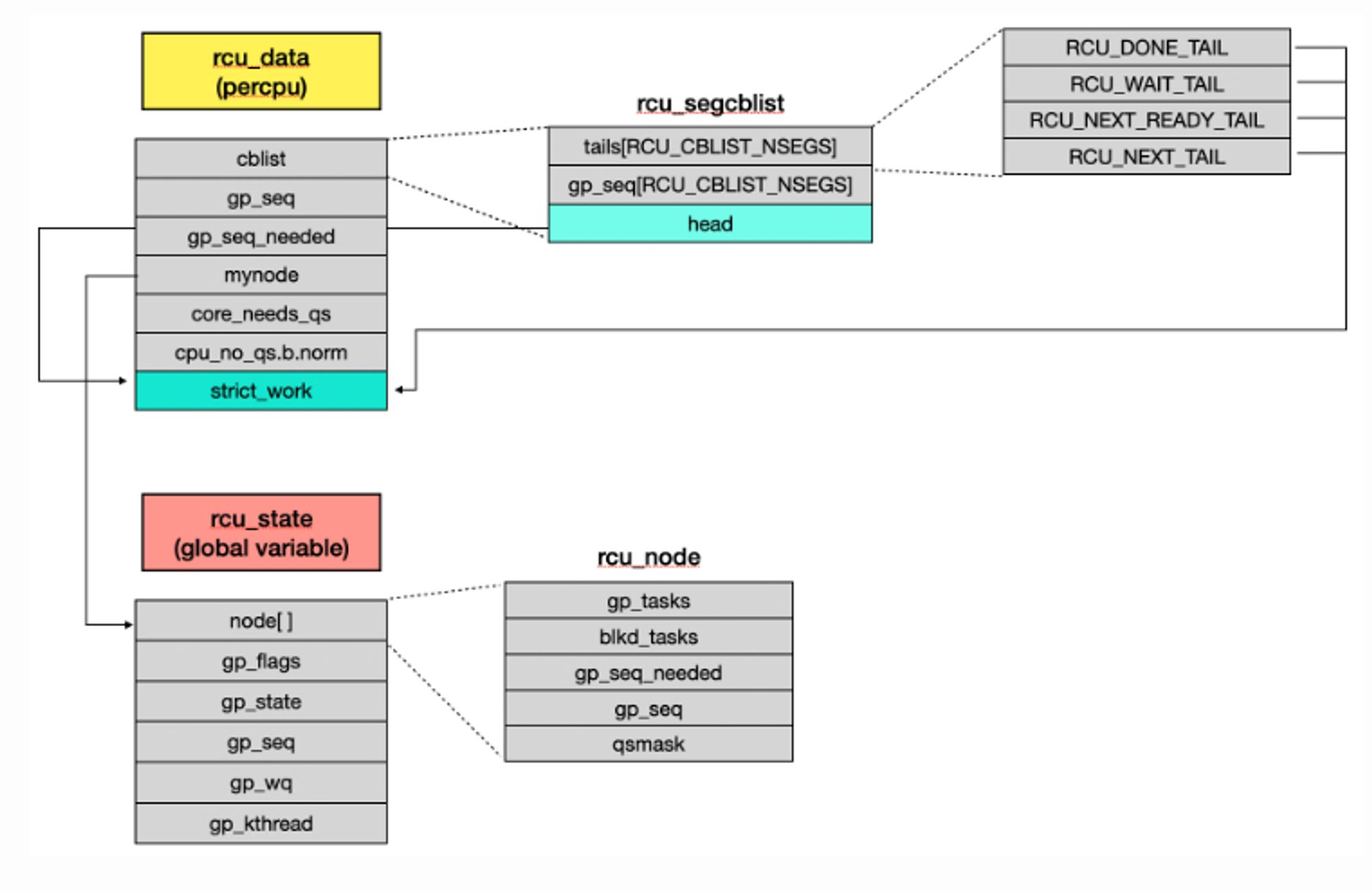
An Introduction to Exploit Reliability: blog.isosceles.com/an-introduct...#exploitation#exploit#cybersecurity#vulnerability
Earlier this year I was invited to give a talk at University of California San Diego (UCSD) for Nadia Heninger's CSE 127 ("Intro to Computer Security"). I chose to talk about modern exploit developmen...
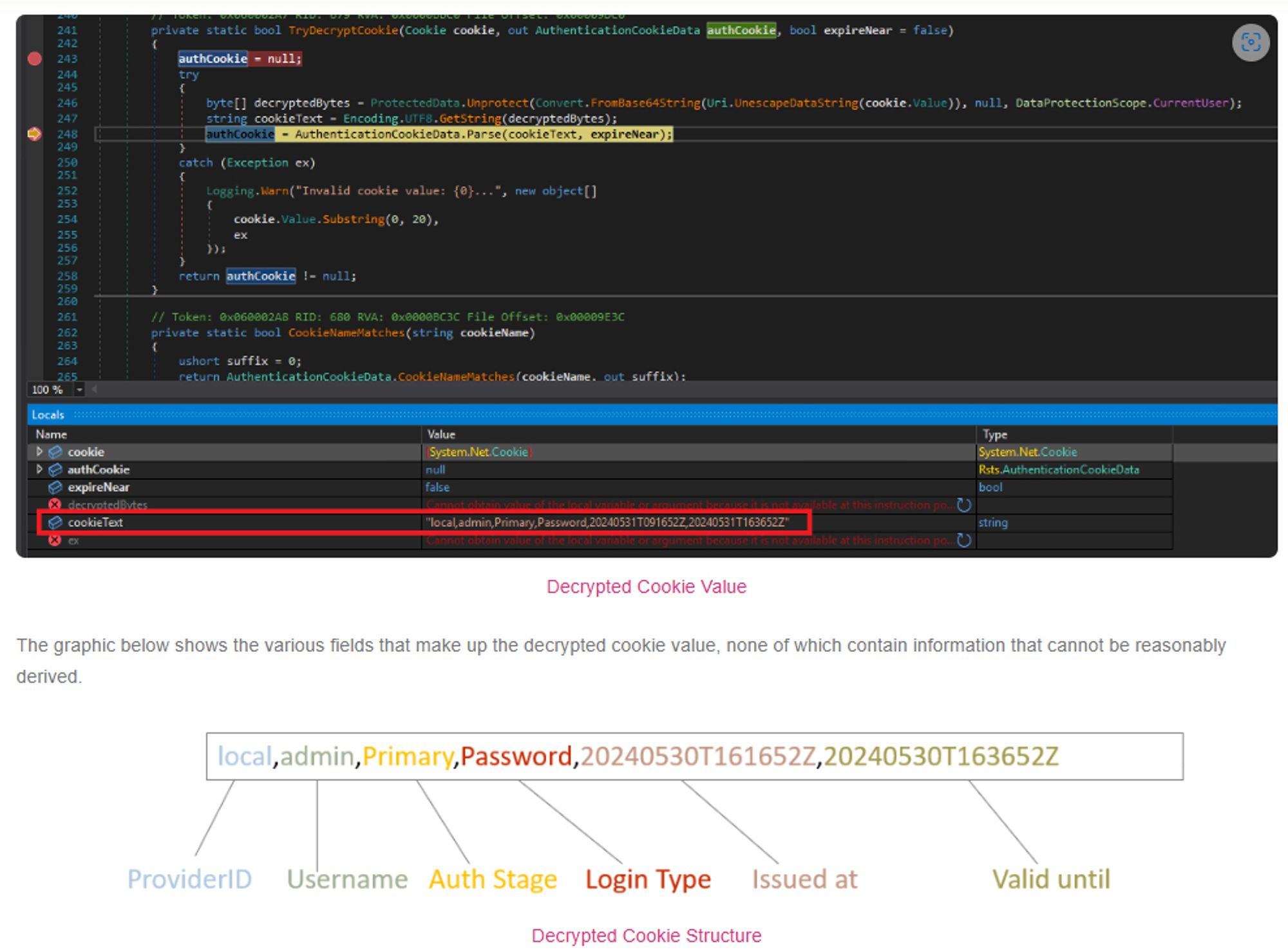
Skeleton Cookie: Breaking into Safeguard with CVE-2024-45488: blog.amberwolf.com/blog/2024/se...#cve#vulnerability#informationsecurity#cybersecurity#cookie
DFIR Breakdown: Impacket Remote Execution Activity – Smbexec: www.cybertriage.com/blog/dfir-br...#impact#infosec#informationsecurity#cybersecurity#dfir#digitalinvestigation#rce
Smbexec is part of the Impacket tools and allows an attacker to remotely launch programs. It's like PsExec, but it uses the SMB protocol to get command
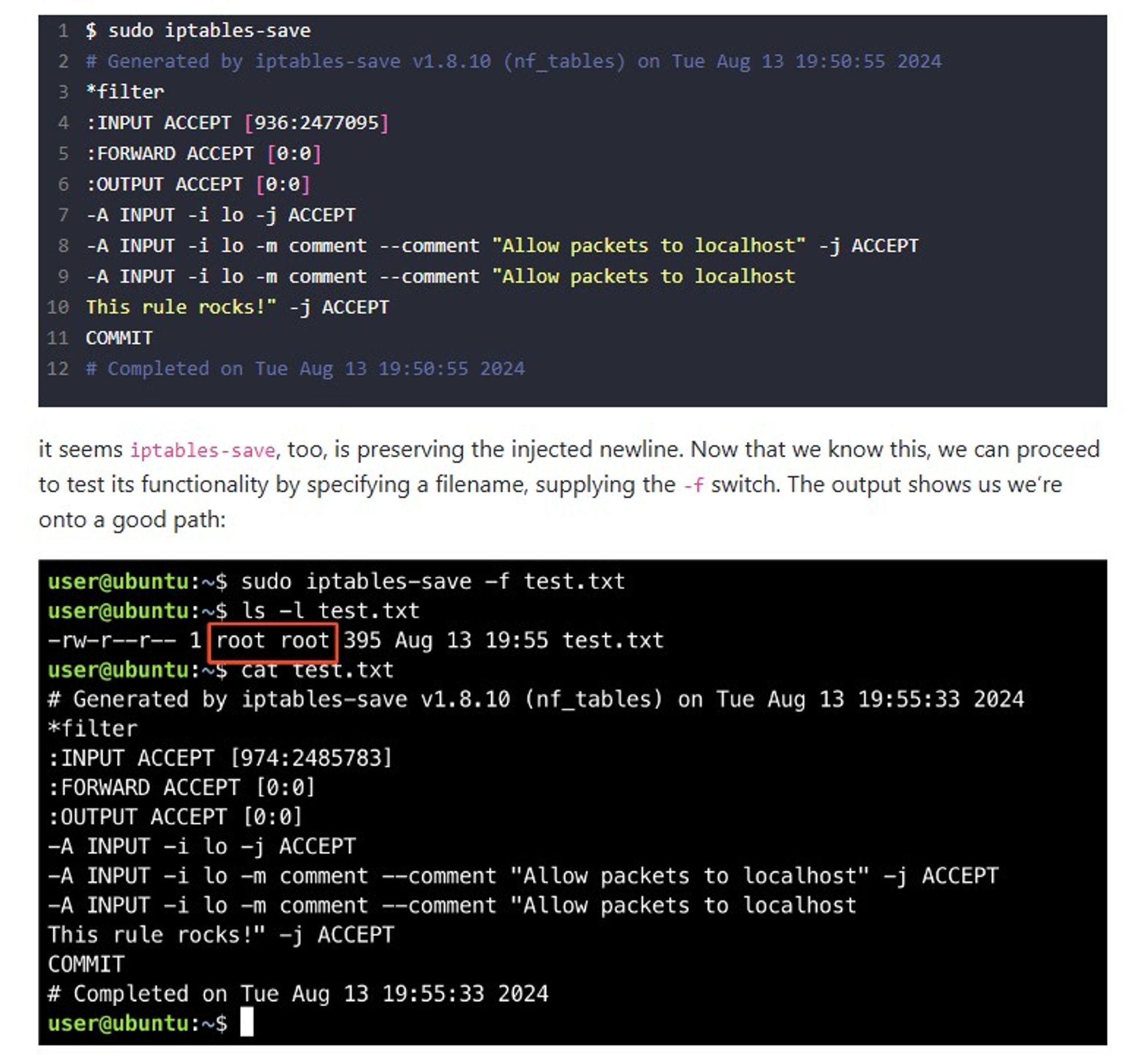
A Journey From sudo iptables To Local Privilege Escalation: www.shielder.com/blog/2024/09...#privilegeescalation#infosec#informationsecurity#linux#iptables#vulnerability#redteam#blueteam
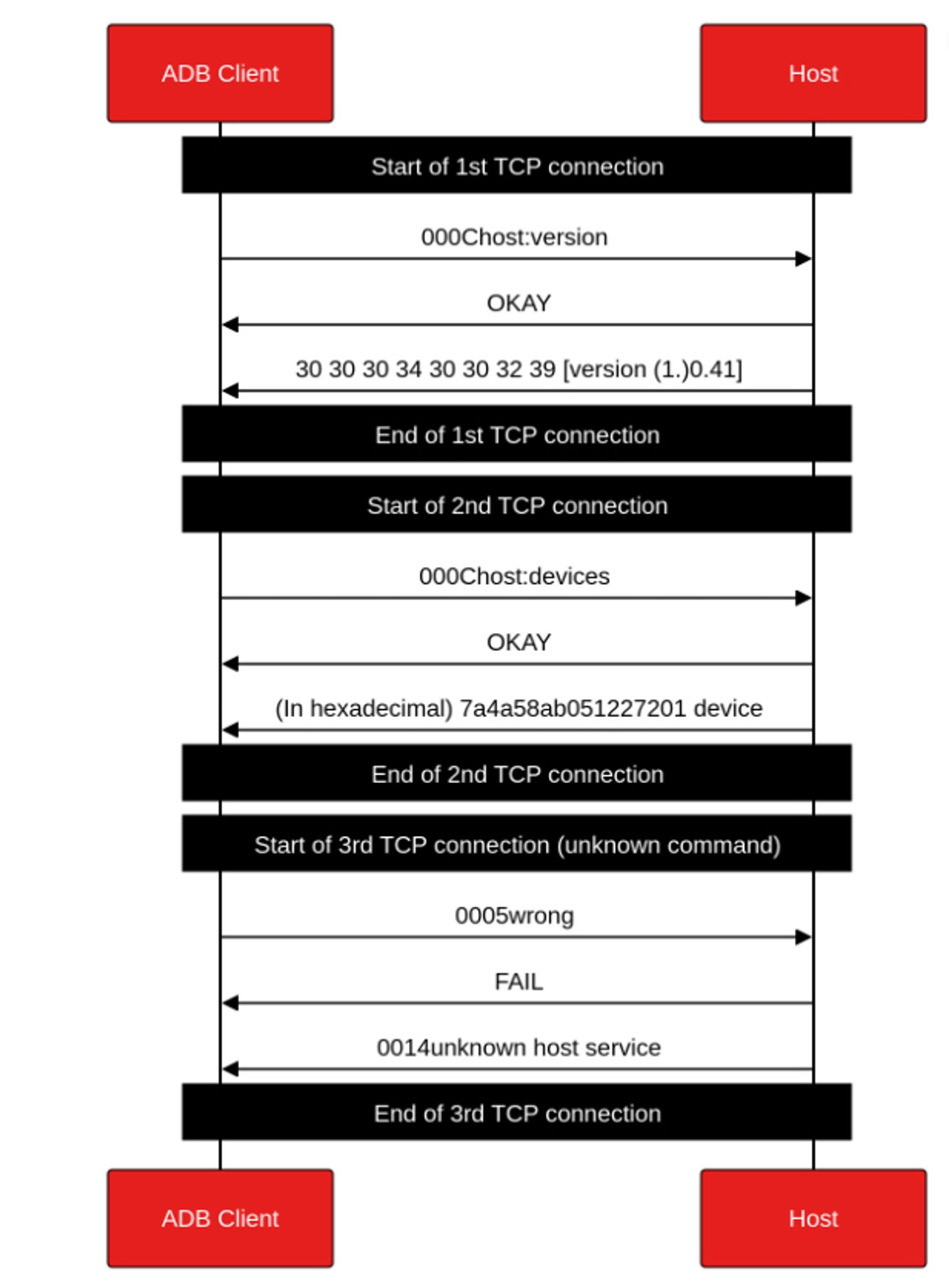
Diving into ADB protocol internals (1/2) www.synacktiv.com/publications...#adb#android#internals#cybersecurity#informationsecurity#mobilesecurity#reverseengineering
Exploit for CVE-2024-8504 & CVE-2024-8503: SQLi and RCE darkwebinformer.com/exploit-for-...#exploit#exploitation#cve#vulnerability#cybersecurity#informationsecurity
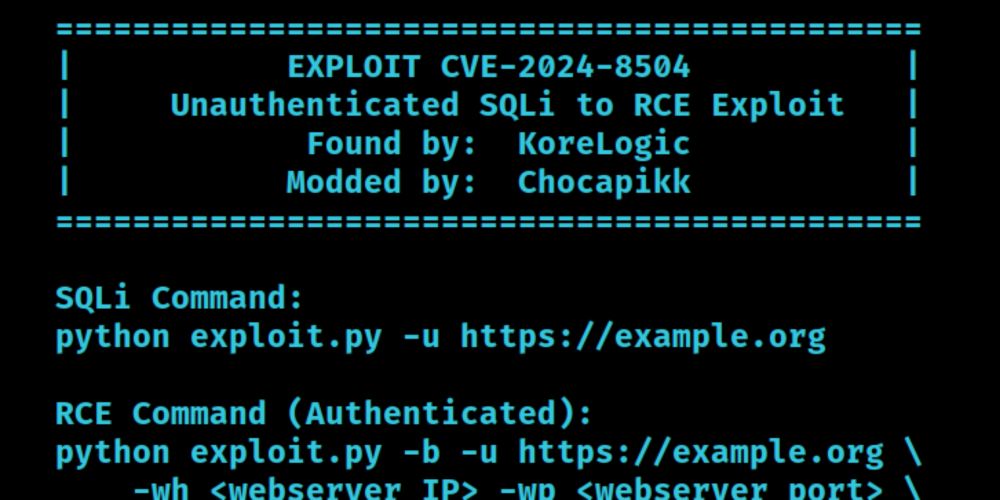
Exploit for CVE-2024-8504 & CVE-2024-8503: SQLi and RCE