This might be the best executed supply chain attack we've seen described in the open, and it's a nightmare scenario: malicious, competent, authorized upstream in a widely used library. Looks like this got caught by chance. Wonder how long it would have taken otherwise.
Fucking wild mastodon.social/@AndresFreun...
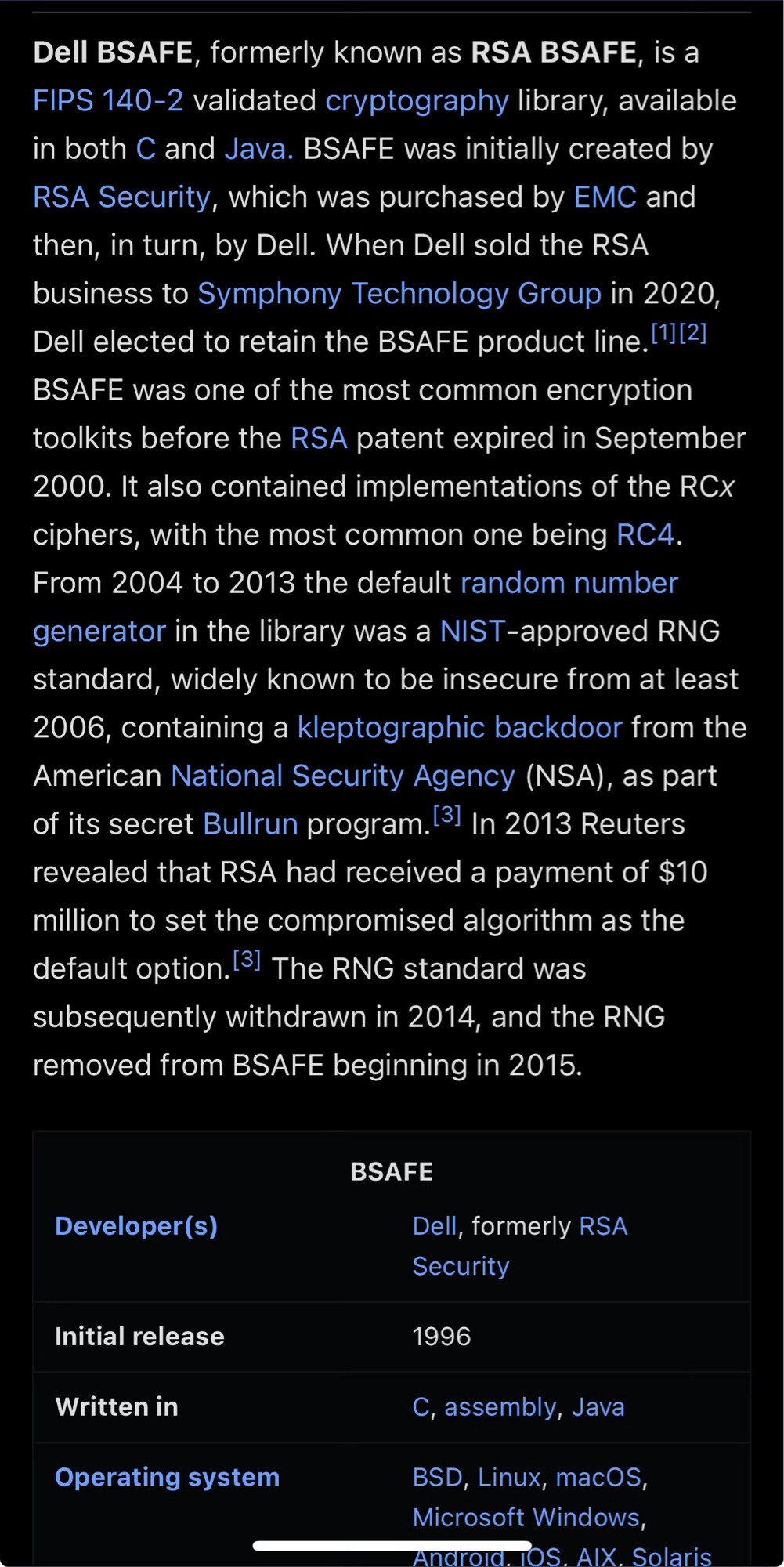
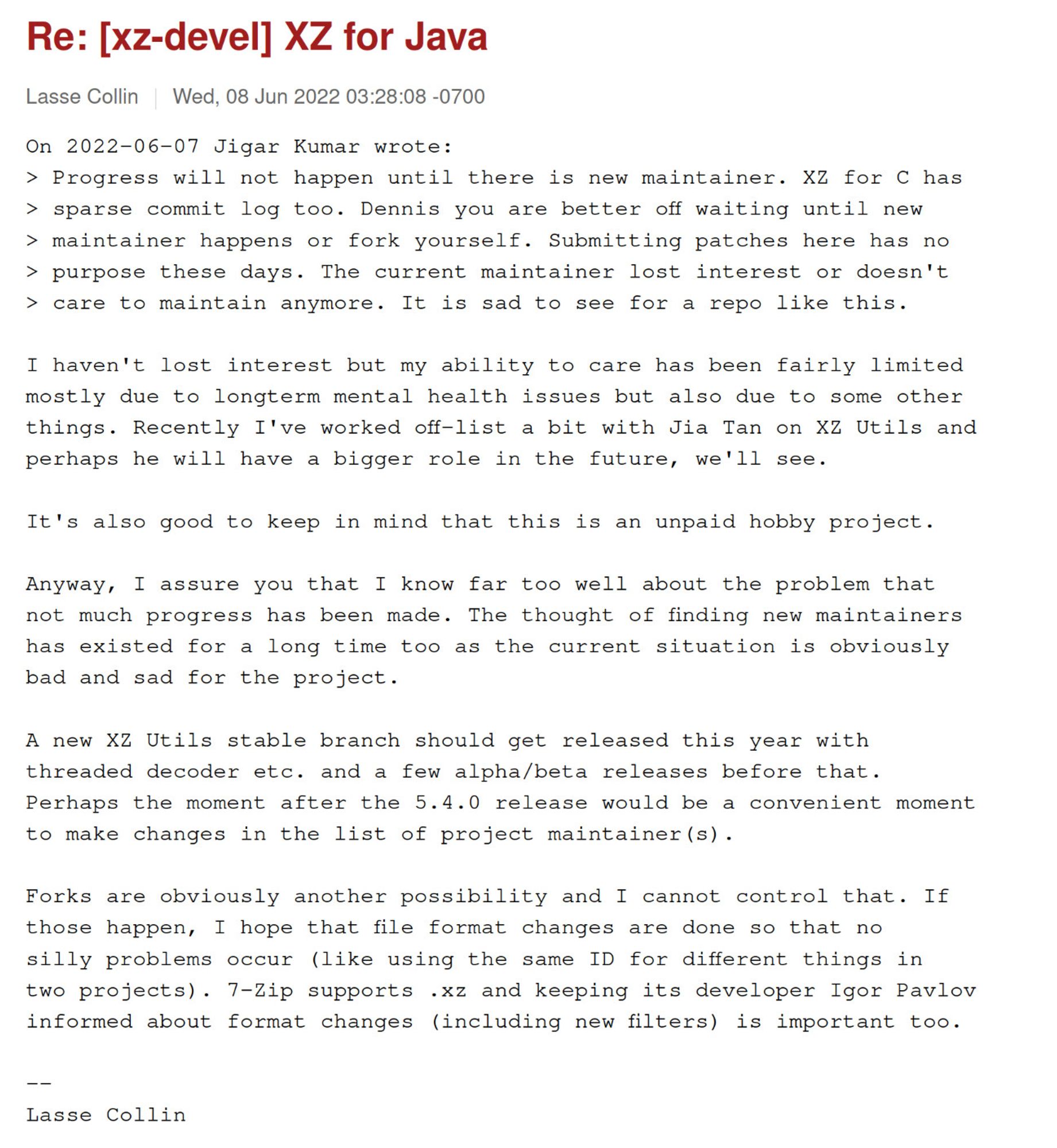
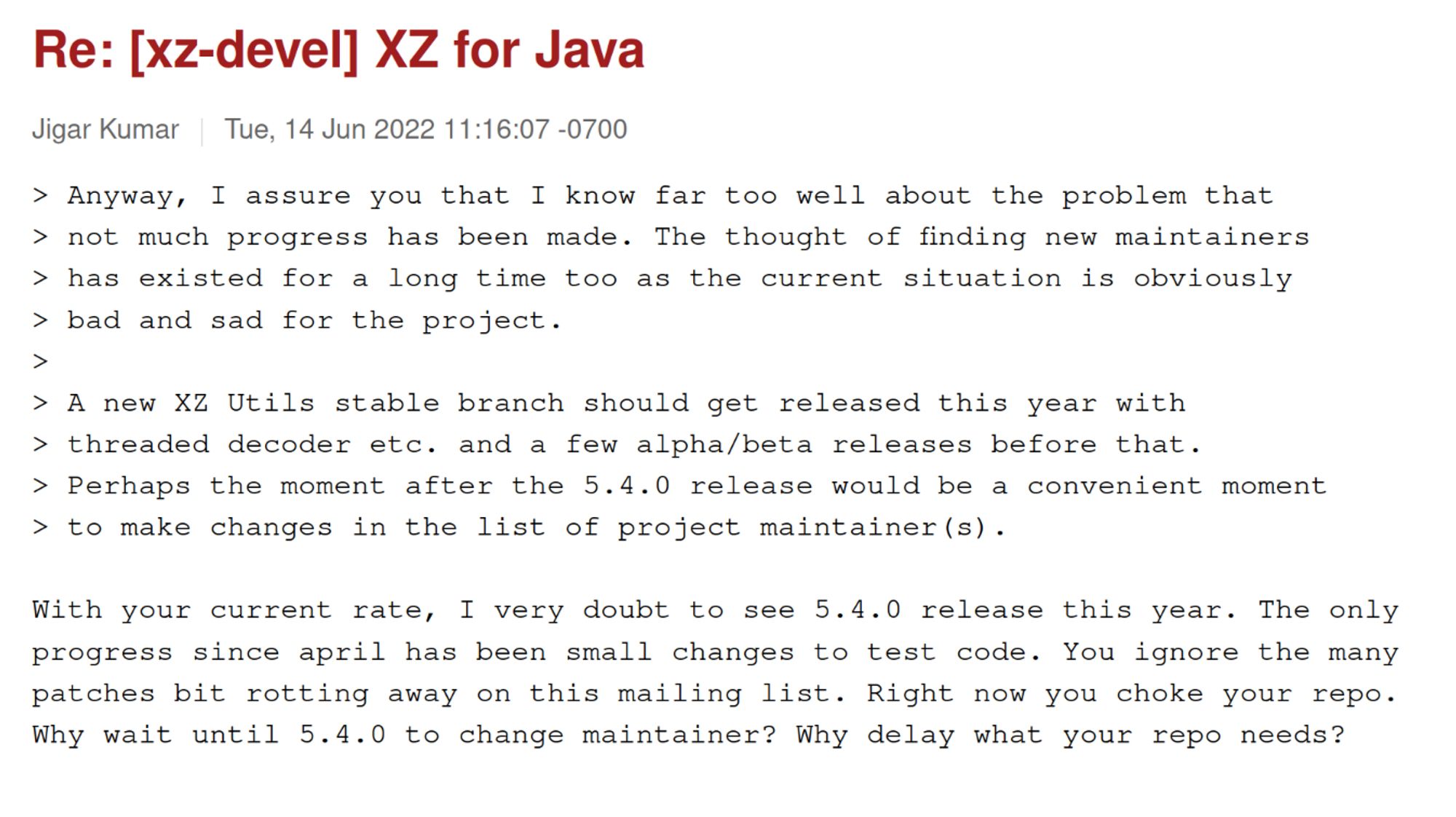
"[...] due to longterm mental health issues but also due to some other things. Recently I've worked off-list a bit with Jia Tan on XZ Utils and perhaps he will have a bigger role in the future" www.mail-archive.com/xz-devel@tuk... pressure in replies 👀 "Why wait until 5.4.0 to change maintainer?"
Yeah ok this was 100% found by sheer luck. mastodon.social/@AndresFreun...bsky.app/profile/look...
Given that the payload hasn't been deciphered yet.. um... isn't this a "change all your passwords, too" thing?
Is there a good summary on this whole thing yet? I’m not a layperson, but I thankfully am not in a position where I have to care too much right now, so I haven’t been following. Curious about who did this, how it was done, how widespread it is, what the consequences are for affected servers.
the thing that's sending me is that this kind of *wasn't* authorized upstream: it was slipped into the tarballs post-source-code-checkout
it's always the night guard idly doing the rounds who just happens to notice the taped-open door latch
There goes my week...

![Hacker News post by formerly_proven:
I think this has been in the making for almost a year. The whole ifunc infrastructure was added in June 2023 by Hans Jansen and Jia Tan. The initial patch is "authored by" Lasse Collin in the git metadata, but the code actually came from Hans Jansen.
> Thanks to Hans Jansen for the original patch.
There were a ton of patches by these two subsequently because the ifunc code was breaking with all sorts of build options and obviously caused many problems with various sanitizers. Subsequently the configure script was modified multiple times to detect the use of sanitizers and abort the build unless either the sanitizer was disabled or the use of ifuncs was disabled. That would've masked the payload in many testing and debugging environments.
The hansjans162 Github account was created in 2023 and the only thing it did was add this code to liblzma. The same name later applied to do a NMU at Debian [truncated]](https://cdn.bsky.app/img/feed_fullsize/plain/did:plc:bvdrfwiamgi5leqs63q2duro/bafkreig5viv47767ru36jtbe5r5b3vbixy6r7m23udnriynsjgelgzt4ze@jpeg)