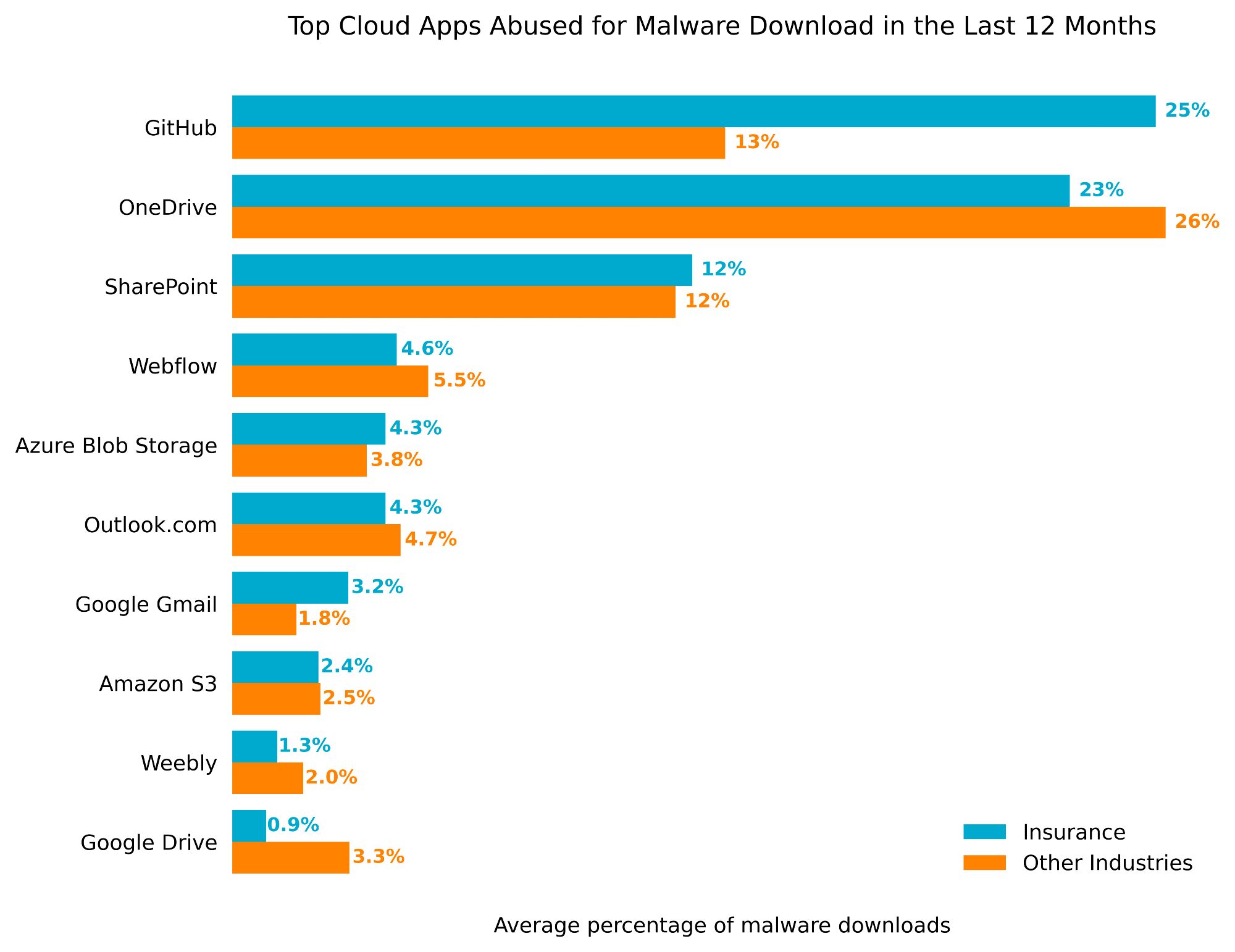
Latest Netskope Threat Labs Report highlights Insurance industry: clown apps serve as a conduit for half of malware downloads, with Grandoreiro banker Trojan and AgentTesla Infostealer most common #potatosecurity#threatintelligence#malwareanalysis www.netskope.com/netskope-thr...
Latest Netskope Threat Labs Report highlights Insurance industry: cloud apps serve as a conduit for half of malware downloads, with Grandoreiro banker Trojan and AgentTesla Infostealer most common #cybersecurity#threatintelligence#malwareanalysiswww.netskope.com/netskope-thr...
The eighth article (62 pages) of Malware Analysis Series (MAS) is available on: exploitreversing.com/2024/08/07/m...#malwareanalysis#macOS#iOS#apple#malware#infosec
The eighth article (62 pages) in the Malware Analysis Series (MAS), a step-by-step malware analysis and reverse engineering series, is available for reading on: (PDF): https://exploitreversing.com/wp-...
The final presentation was See et al.'s "Binary Sight-Seeing: Accelerating #ReverseEngineering#POIswww.acsac.org/2023/p...#MalwareAnalysis#IDAPro#Ghidra#Botnets
youtu.be/PzY-FF_M-zM#cybersecurity#AI#riskmanagement#incidentresponse#phishing#malwareanalysis
Imagine a world where cyber threats are evolving at a pace so rapid that traditional defenses struggle to keep up. In this high-stakes environment, cybersecu...
I have been slowly writing the next articles: 1. MAS 08: Introduction to MacOS malware analysis. 2. ER 03: macOS/iOS (part 01) 3. MAS 09: Shellcode Analysis 4. ER 04: Browsers (part 01) 5. RE 05: Hypervisors (part 01) exploitreversing.com#vulnerability#exploitation#malwareanalysis

Follow My Blog Get new content delivered directly to your inbox.
CISA's Malware Analysis Platform Could Foster Better Threat Intel www.darkreading.com/vulnerabilit...#Infosec#Security#Cybersecurity#CeptBiro#CISA#MalwareAnalysis

But just how the government differentiates its platform from similar private-sector options remains to be seen.
Toolkit - The Essential Toolkit For Reversing, Malware Analysis, And Cracking www.kitploit.com/2024/04/tool...#Infosec#Security#Cybersecurity#CeptBiro#Toolkit#EssentialToolkit#Reversing#MalwareAnalysis#Cracking
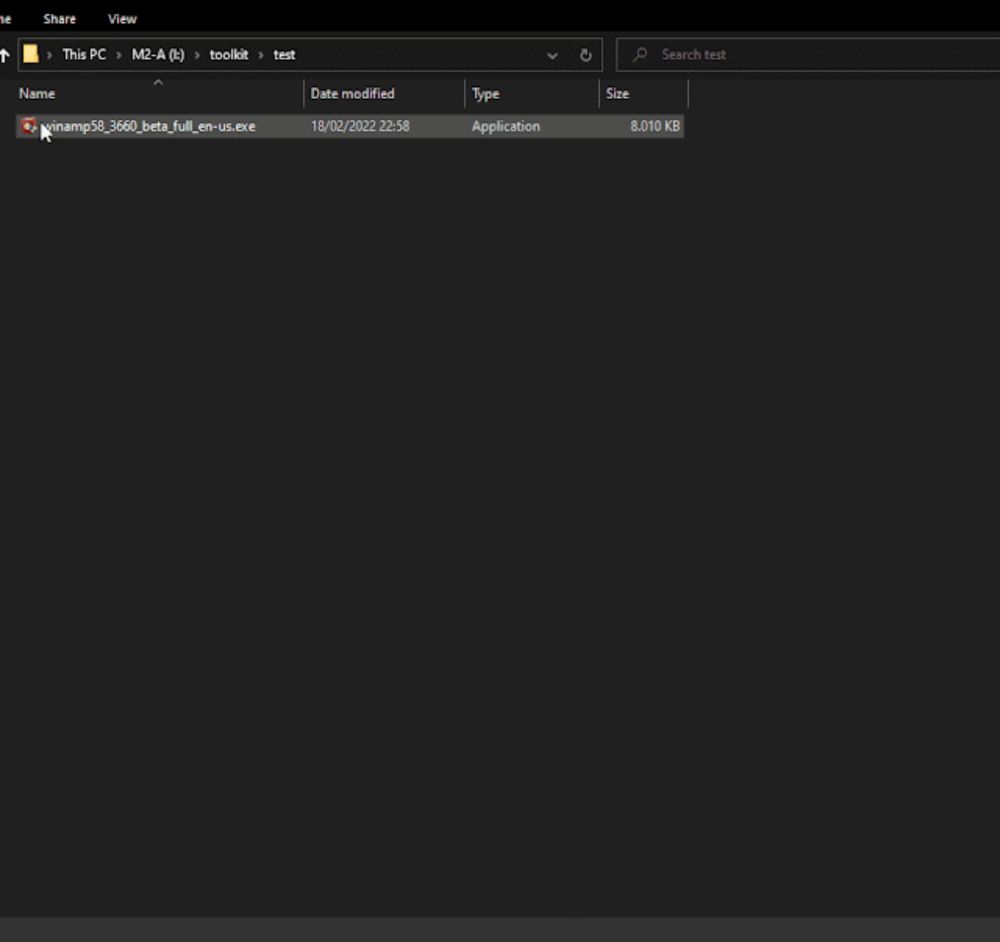
This tool compilation is carefully crafted with the purpose of being useful both for the beginners and veterans from the malware analysis ...
Reverse Engineering Snake Keylogger: Full .NET Malware Analysis Walkthrough any.run/cybersecurit...#Infosec#Security#Cybersecurity#CeptBiro#ReverseEngineering#Snake#Keylogger#.NET#MalwareAnalysis

Discover an in-depth analysis of the Snake Keylogger malware, exposing its config, infostealing features, and anti-analysis techniques.